In today's digital age, security is a major concern for individuals and organizations alike. With the increasing number of cyberattacks and data breaches, it’s crucial for developers to have a thorough understanding of security best practices. The security of an application is of the utmost importance, as it can directly impact the safety and privacy of users' data.
The growth and speed of cloud-native development have resulted in an expanding attack surface filled with vulnerabilities that, if left unchecked, could result in damage to the reputation of the organization responsible for the application. By designing and developing secure applications, you can protect sensitive data and prevent potential data breaches.
So, how can you raise the bar and level up your security skill set? In this blog, you'll use the capabilities of the New Relic observability platform to detect and remediate issues in Juice Shop, a deliberately insecure web application from OWASP. The application is available as a public repository on GitHub and is typically used in security trainings, awareness demos, CTFs, and as a guinea pig for Security RX security tools. You’ll also learn how New Relic can help you to detect some of the OWASP Top Ten vulnerabilities and other security flaws found in real-world applications.
Application monitoring for identifying vulnerabilities in real time
As the cornerstone of the New Relic observability platform, application performance monitoring (APM) can give you real-time insights into the performance and behavior of your applications. This includes information on response times, error rates, and transaction traces. These can help you to quickly identify security vulnerabilities or potential threats.
High error rate
You can use APM to detect error rates, and an unusually high amount of errors is typically an indicator that something unexpected is happening within your application. For example, high error rates could be caused by hack bots trying to find open paths into an application. Using the OWASP Juice Shop example, if you use the developer tools in your browser to inspect the network activity, you’ll see a request to http://20.237.100.141:3000/api/Challenges/?name=Score%20Board.
If you call this URL, you’ll get additional information about this scoreboard within Juice Shop. Check this out in the next screenshot.
This screenshot shows one of the so-called “red flags” that should tip you off to a security issue in the Juice Shop app. Without giving too much away, here's a hint: if you try to guess what the URL of the hidden scoreboard is, you’ll discover information about how adversaries would also try to identify and probe certain parts of your application.
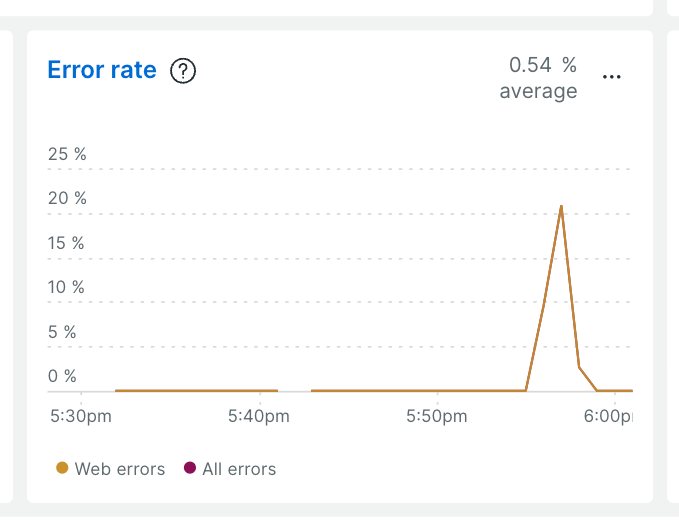
Adversaries can and will scan your application for such open doors. You can identify this bot crawling by looking at peaks in error rates in New Relic APM.
Error tracking
Similar to the high error rate issue you just learned about, let’s have a look at another example using error tracking, a key capability of New Relic. By tracking detailed information on application errors, you can quickly identify and resolve issues that could be exploited by adversaries.
For example, if an application is throwing errors related to input validation, it could indicate a potential vulnerability. With New Relic, you can quickly identify the root cause of the errors and take action to resolve the issue, reducing the risk of an attack.
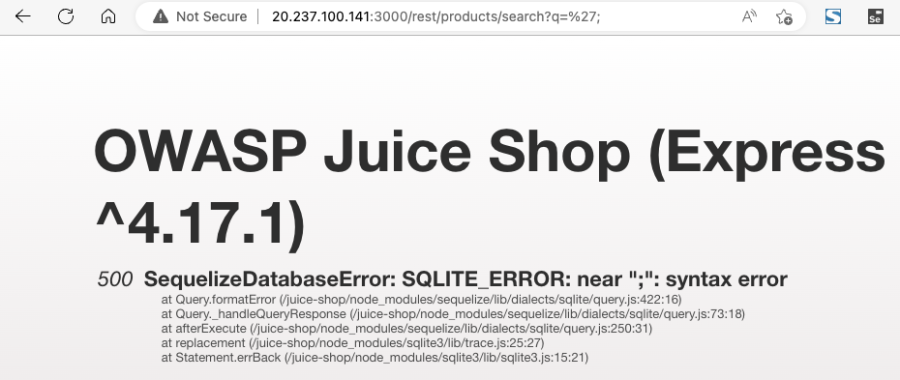
In the next screenshot, look at the two SequelizeDatabaseError exceptions that occurred.
The error message that is captured refers to the SQL Lite errors:
SQLITE_ERROR: incomplete input
and
SQLITE_ERROR: near ";": syntax error
Do these error messages somehow look familiar? Any idea of what a potential adversary is trying to achieve? Yes, you’re right, this seems to indicate that there is a potential SQL injection issue in our code.
So, let’s step back a little bit and have a look at the application. When reviewing the requests in the network tab of your browser's developer tools, you should see a GET request to http://20.237.100.141:3000/rest/products/search?q=.
So it seems like you could potentially use this endpoint to retrieve product information. Indeed, you can run a request to http://20.237.100.141:3000/rest/products/search?q=orange to retrieve all products with the given search criteria.
What if you now add '; as the search criteria? Well, we get a SQL exception.
From the point of view of a potential adversary, this indicates that SQL injection is indeed already possible.
Play with this a little more and try using '-- as the search criteria. The entire request URL is now http://20.237.100.141:3000/rest/products/search?q='--.
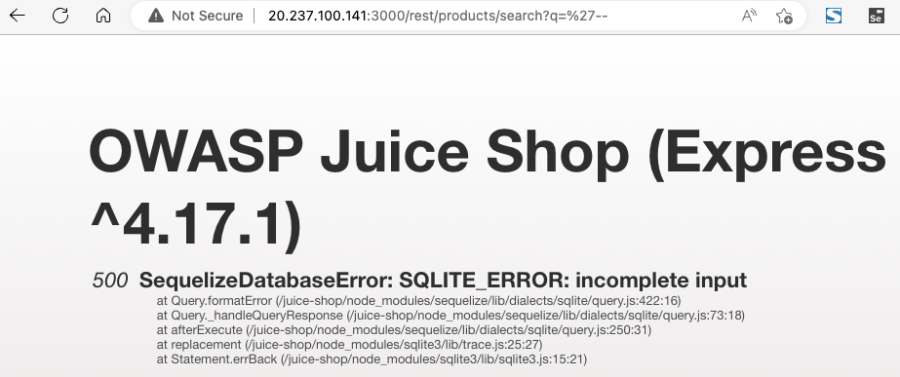
Again, another exception. This error is happening because of two (now unbalanced) parentheses in the query.
Updating the search criteria to '))-- fixes the syntax and successfully retrieves all products, including a deleted Christmas offer. The entire request URL is now http://20.237.100.141:3000/rest/products/search?q='))--.
Of course, the example above in itself is not really dangerous, unless I am now also able to order any hidden items. But, imagine adding some more damaging requests that could potentially destroy your entire shop and customer database.
Common vulnerabilities and exposures (CVEs)
The New Relic Security RX capability helps you overcome security blindspots within your applications. Modern software is composed of thousands of components, and legacy security offerings don’t give security teams or individual developers the necessary insight to monitor and remediate vulnerabilities these components introduce. Security RX provides a birds-eye view of all your software's vulnerabilities so you can:
- Identify the most urgent vulnerabilities.
- Calculate the vulnerability surface area of your software.
- Triage and assign vulnerabilities to users with explicit remediation steps provided.
For example, if a library used by an application is found to have a known vulnerability, New Relic will alert you and provide information on the specific CVE, so you can update or patch the library as necessary to avoid potential security breaches.
This additional security capability of the New Relic APM agent makes it easier for you to maintain the security of your applications and address vulnerabilities found in dependent open source libraries you’re using. New Relic even provides information on how to remediate vulnerabilities by upgrading vulnerable libraries to newer versions. Easily learn how to get started with Security-RX with us.
Synthetic monitoring for simulating vulnerabilities
Synthetic monitoring is a New Relic capability that can simulate user behavior and test the performance of your applications. With this simulation, you can identify potential security issues and vulnerabilities.
Testing access to sensitive information
For example, if a simulated user is able to access sensitive information without proper authentication, it could indicate a security vulnerability. With synthetic monitoring, you can quickly identify the issue and take action to resolve it, reducing the risk of a security breach.
New Relic synthetic monitoring allows you to create automated scripted tests that can be used to proactively monitor your applications and services. However, you can also write tests that check for issues or vulnerabilities in your application. Let’s have a look.
In the next image you'll see a synthetic check created with the New Relic scripted browser that accesses the application and tries to log in with some unsafe or hijacked admin credentials.
The check is successful when the login is not possible with the given credentials, and the check fails when the login is successful and the script is able to access the administrator account.
Conclusion
Adding security to your skill set is crucial in today's digital age. Not every software developer is—and some may never be—an application security expert. However, due to the increasing focus on security and the risks involved, it is becoming more and more important to start adopting a security mindset.
Next steps
New Relic is a powerful platform that can help you enhance your security knowledge and skills with capabilities like application monitoring, error tracking, and synthetic monitoring. Check out how you can uplevel your skills today by signing up for a free, full-access account.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.




