In another important step for the New Relic all-in-one observability platform, we're pleased to announce the availability of New Relic interactive application security testing (IAST). As DevOps teams build and ship software faster than ever before, 85% of applications still contain vulnerabilities. The current state of application security testing practices is inaccurate and disjointed—resulting in false positives, missed release cycles, and increased security costs.
New Relic IAST goes beyond current approaches, by providing real-time visibility and context into security findings, unmatched detection accuracy with near zero false positives and proof of exploit, and guided remediation. The New Relic patented deterministic technique provides automated vulnerability validation via real-world attack simulation, enabling you to focus on high-priority security risks and confidently ship code faster. Additionally, New Relic IAST is fully integrated with New Relic Security RX, allowing you to continuously find, fix, and verify high-risk vulnerabilities across the software development lifecycle.
New Relic IAST is available in both the North American and EMEA service regions as part of our all-in-one observability platform experience. Key capabilities include:
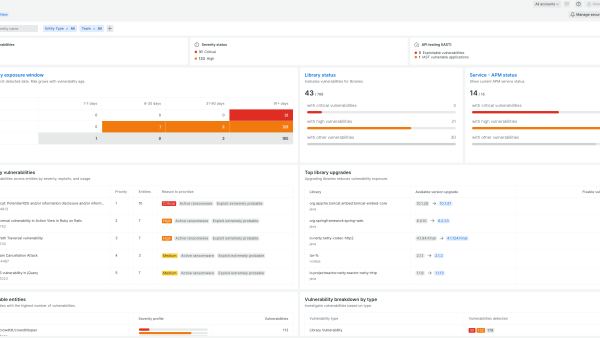
- 360 visibility: View the application stack and associated relationships with context-driven insights to eliminate blind spots and validate remediation efforts.
- Near-zero false positives: Ensure teams focus on real security risks with unmatched detection accuracy, risk-based prioritization, and automated vulnerability validation.
- Proof of exploit: Find, fix, and verify exploitable vulnerabilities with proof of exploit via dynamic assessment capabilities that pinpoint the source of vulnerabilities by simulating real-world attacks.
- Guided remediation: Help developers avoid critical mistakes across the application lifecycle with remediation steps, guardrails, and status tracking.
See and secure everything you build and run
As the saying goes, “You can’t protect what you can’t see.” This is especially true when it comes to securing applications. With New Relic IAST, you can now see all protected and unprotected applications, which eliminates blind spots and hidden threats. Comprehensive dashboards provide complete visibility into high-priority vulnerabilities, from applications to their components and APIs. Detailed test results and visualizations provide insights into application security posture and trends against compliance standards such as OWASP Top 10 and more.
Accurately pinpoint where vulnerabilities exist
Now you can identify vulnerabilities faster across all layers of the application stack in real time, reducing false positives with fast, accurate detection of real security risks. With New Relic IAST, developers can take immediate action with a risk-prioritized list of verified vulnerabilities. New Relic IAST quickly processes thousands of HTTP/HTTPS requests, identifies vulnerabilities, and reduces alert fatigue with near zero false positives. It provides accurate out-of-the-box results with detailed vulnerability descriptions and detections down to the line of code. Having these capabilities fully integrated into the New Relic observability platform enables you to focus on what matters most for faster remediation and improved productivity.
Find, fix, and verify vulnerabilities with proof of exploit
With New Relic IAST you can save valuable time by testing vulnerabilities and validating whether they are real with proof of exploit—enabling you to focus on verified vulnerabilities and ship code faster.
Identified vulnerabilities are verified via real-world attack simulation to validate if the vulnerability is exploitable. Having proof of exploit confirms the severity of the vulnerability by providing information that’s considered confidential and should not be accessible. Additionally, engineering teams can now leverage and correlate security and observability data for enhanced context, to improve the effectiveness of remediation.
Remediate vulnerabilities faster than ever
Remediating security issues just got easier. You don’t need to be a security expert when you use guided remediation and guardrails from New Relic experts that help you avoid critical mistakes that could lead to a potential security incident.
Our comprehensive analysis contains all required information, including explanation of risk, technical description, code location, and more. It also integrates seamlessly with Jira, so you can easily track and monitor the status of your remediation efforts. Step-by-step guidance ensures developers can take immediate action to eliminate vulnerabilities and prevent them from spreading across programming libraries. New Relic IAST helps guide, speed up, and track remediation efforts while providing a continuous feedback loop to ensure you can build more secure code.
Our team has historically relied on traditional, complex tools to identify security risks, causing us to spend a lot of time and resources to find and fix vulnerabilities before they could impact our business and our customers.
New Relic IAST empowers our developers to code with confidence by automating work and providing a comprehensive view of security risks, including real-time feedback, accuracy, and context-aware security analysis—all in the context of our observability practice and without impeding the development process.
This enables our team to prioritize security and observability, helping them identify risks earlier in the development lifecycle and deliver a better experience for our customers.
Get started today with New Relic IAST
If you have a free New Relic account, you already have access to New Relic IAST if you’re using a supported agent. To learn more, contact your New Relic account representative and get started.
Don’t have a New Relic account yet? Sign up for free today. Your free account includes 100 GB/month of data ingest and one full user.
Forward-looking statements
This blog post contains “forward-looking” statements, as that term is defined under the federal securities laws, including but not limited to statements regarding New Relic Interactive Application Security Testing, and its capabilities and anticipated benefits related thereto. The achievement or success of the matters covered by such forward-looking statements are based on New Relic’s current assumptions, expectations, and beliefs and are subject to substantial risks, uncertainties, assumptions, and changes in circumstances that may cause New Relic’s actual results, performance, or achievements to differ materially from those expressed or implied in any forward-looking statement. Further information on factors that could affect New Relic’s financial and other results and the forward-looking statements in this press release is included in the filings New Relic makes with the SEC from time to time, including in New Relic’s most recent Form 10-K, particularly under the captions “Risk Factors” and “Management’s Discussion and Analysis of Financial Condition and Results of Operations.” Copies of these documents may be obtained by visiting New Relic’s Investor Relations website at http://ir.newrelic.com or the SEC's website at www.sec.gov. New Relic assumes no obligation and does not intend to update these forward-looking statements, except as required by law.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.