In our digital realm, applications drive businesses forward, fueling everything from behind-the-scenes tasks to frontend user engagement. Yet, this also means they’re prime targets for cyber threats. With each added feature and code integration, vulnerabilities could sneak in. So, it’s not about wondering whether someone might try exploiting your apps; it's a matter of when. Here’s where application security management shines, acting as your virtual shield. Dive into this guide as we unpack how you can empower your applications to stand tall against even the most persistent digital adversaries.
What is application security management?
Think of application security management as your proactive plan. It zeroes in on identifying, patching up, and averting software application vulnerabilities. The mission? Bolstering application security across its lifecycle—from the drawing board to routine maintenance. The ultimate aim? Shielding apps from potential threats that can lead to data leaks or hiccups in services.

Understanding application security risks
In this cloud-driven, interconnected era, getting a handle on application security is paramount. As the software world pivots towards cloud-native apps and embraces container-rich environments, the risk horizon broadens. It's not just about safeguarding data and ensuring users trust you; it's about navigating challenges posed by today's software development models. Let's spotlight the risks that might jeopardize application integrity and trace back to where these risks originate.
Potential risks in application security
- SQL injection hits: Attackers might exploit application features, leading to unauthorized data tweaks or access.
- Cross-site scripting (XSS) raids: Malicious scripts, when added to web pages, can put user data at risk.
- Distributed-denial-of-service (DDoS) onslaughts: Overpowering an app’s resources, rendering it inaccessible to genuine users.
Where do these risks come from?
- Hasty coding: Can inadvertently open doors for attackers.
- Overlooking security in the early stages: Leaves the software exposed to threats.
- Not updating software: Lets known vulnerabilities persist.
- Lax security controls: Poor access rules and missing encryption can make apps an easy target.
- Relying on open-source components without vetting: May invite unforeseen threats.
- Growing complexity in software: As applications evolve and intertwine, the attack scope broadens.
- Software glitches and misconfigurations: Unauthorized users could gain access to classified data.
The role of application security management in risk mitigation
Effective application security management is your compass to safer waters. Through regular vulnerability checks, businesses can anticipate and fix weak points. Pair this with an incident response blueprint, and you’re equipped to tackle breaches head-on. Training developers in security best practices? That's your ticket to minimizing vulnerability risks.
Seven steps to building an effective application security management strategy
Cyber threats are craftier than ever. That’s why a solid game plan for application security—spanning its entire lifecycle—is non-negotiable. While your strategy might vary based on specific app needs and organizational priorities, here's a universal blueprint:
- Embed security early on: Initiate with security steps right from the get-go. Make security a foundational pillar, not an afterthought.
- Model potential threats: Predict possible vulnerabilities to design with safety in mind.
- Adopt secure coding protocols: Create and stick to coding standards that keep vulnerabilities at bay.
- Review code regularly: Continuous checks help identify and address potential hiccups before the big launch.
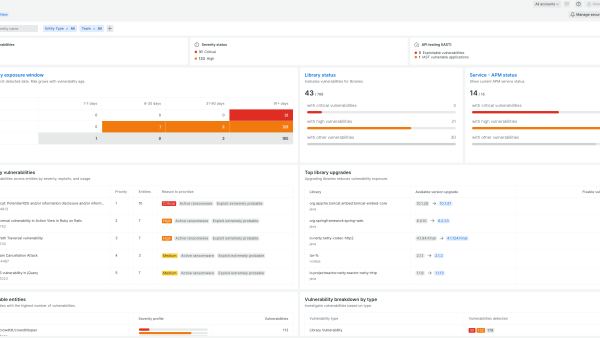
- Execute vulnerability checks: Employ diverse tools to pinpoint and fix potential security loopholes.
- Champion minimum access: Offer only essential access rights to reduce potential damages from compromises.
- Have an incident response plan: Craft an incident response strategy to respond swiftly and effectively to security breaches. Speedy actions can contain the chaos.
Test and monitor application security with New Relic IAST
As the terrain of application security shifts, interactive application security testing (IAST) stands out. Experience the magic of New Relic IAST—a unique solution for crafting secure apps and accelerating code deployment. With New Relic IAST you can seamlessly spot, solve, and validate high-risk vulnerabilities ahead of time. Trust in our vision, and let's build safe, efficient applications together.
Next steps
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.