In an era where data breaches and cyberattacks are commonplace, the role of secure code has never been more critical. Businesses, governments, and individuals are increasingly dependent on digital platforms for a variety of tasks. This reliance makes the software that powers these platforms a prime target for cybercriminals. The challenge lies in balancing the need for rapid deployment with robust security measures. This guide walks you through the strategies and tools that can help you achieve this balance, allowing you to ship secure code fast without compromising on security.
Understanding code vulnerabilities
What are code vulnerabilities?
Code vulnerabilities are essentially the Achilles' heel of software systems. They’re the flaws or weaknesses that can be exploited to compromise the system's security. These vulnerabilities can arise from a variety of factors, including poor coding practices, lack of input validation, and outdated libraries or dependencies.
Common types of vulnerabilities in code
- Remote code execution (RCE): This critical and prevalent vulnerability in software development allows an attacker to execute arbitrary code on a target system, typically with elevated privileges. This vulnerability arises when an application either directly executes user input as code or allows the input to be part of a system command. When an attacker successfully exploits an RCE vulnerability, they can perform malicious actions such as stealing sensitive data, deleting files, or installing malware, often leading to a full compromise of the system.
- Injection attacks: These attacks involve inserting malicious data or code into a software system. For instance, SQL injection attacks target databases by inserting malicious SQL code via input fields, potentially revealing sensitive data.
The impact on application security and user data
When vulnerabilities are exploited, the consequences can be severe. Unauthorized data access can lead to sensitive information being leaked, while data corruption can render an application useless. In extreme cases, vulnerabilities can even allow attackers to take over a system, leading to a wide range of malicious activities. Beyond the immediate threat of unauthorized access or system crashes, vulnerabilities can have long-term repercussions. Data breaches can erode customer trust, result in financial losses, and even lead to legal consequences. Moreover, repairing the damage from an exploited vulnerability—both in terms of system integrity and brand reputation—can be a lengthy and costly process.
Secure code development best practices
Principle of secure coding
Secure coding isn't just about preventing attacks; it's about building software that’s resilient by design. This means anticipating potential threats and designing systems that can withstand them, even in unforeseen circumstances. Integrating security testing early in the software development lifecycle (SDLC) is crucial to building resilient software. Early and continuous testing, often referred to as "shift-left testing," allows developers to identify and address vulnerabilities and security issues from the inception of a project, rather than at the end. Security should be an integral part of the development process, reducing the risk of late-stage disruptions and potential delays in deployment. By incorporating security considerations and testing throughout the SDLC, developers can create software that is not only secure but also robust and reliable, capable of withstanding both current and emerging threats. This holistic approach to security fosters the development of software that is inherently resilient, safeguarding both users and organizations from the evolving landscape of cyber threats.
Secure coding guidelines and standards
- OWASP Top 10: The Open Web Application Security Project (OWASP) regularly publishes a list of the top 10 most critical web application security risks. This list serves as a starting point for organizations looking to bolster their web application security.
Input validation and sanitization techniques
- Whitelisting vs. blacklisting: While blacklisting involves blocking known malicious inputs, whitelisting is a more restrictive approach that only allows specific, known-safe inputs. Whitelisting is generally considered more secure because it doesn't rely on predicting all possible malicious inputs.
- Sanitization: Before processing any user input, it's crucial to sanitize it. This means stripping out any potentially harmful data that could be used in an injection attack or other exploit.
Secure handling of sensitive data
- Encryption: Data encryption transforms sensitive information into a coded format, ensuring that only authorized parties with the decryption key can access the original data.
- Hashing: Especially important for passwords, hashing converts data into a fixed-size string of characters, which typically appears random. Unlike encryption, hashing is a one-way process.
Proper error and exception handling
- Avoid detailed error messages: Errors are inevitable in software development. However, how a system responds to those errors can make all the difference in terms of security. Revealing too much information in error messages can provide attackers with valuable insights, while failing to handle exceptions properly can leave systems vulnerable to crashes or exploits.
Secure configuration management
- Principle of least privilege: This principle, also known as PoLP, involves providing only the permissions necessary to perform a task, thereby limiting the potential for misuse.
Secure coding tools and technologies
Overview of secure coding tools
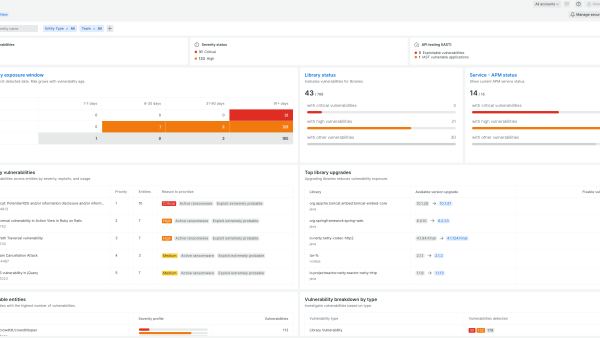
In the battle against vulnerabilities, developers have an arsenal of tools at their disposal. Among these, New Relic stands out as a comprehensive solution that not only monitors application performance but also provides insights into potential security threats. With its suite of observability and security capabilities, New Relic offers an integrated approach to identifying and rectifying vulnerabilities.
Static code analysis tools
Static application security testing (SAST) analyzes the source code, bytecode, or binary code of an application without executing it. It looks for patterns or code constructs that are indicative of potential security vulnerabilities.
- SonarQube: Scans your codebase for vulnerabilities and provides detailed reports, helping you to fix issues before they become a problem.
- Snyk Code: Analyzes the source code of applications to identify security vulnerabilities and provides actionable insights to developers to remediate those issues.
Static code analysis with New Relic: The New Relic observability platform allows for integration with tools like SonarQube, providing a seamless environment to scan a codebase, identify potential vulnerabilities, and ensure adherence to best practices.
Dynamic code analysis tools
Dynamic application security testing (DAST) tests the application in its runtime environment, simulating how an attacker might exploit potential vulnerabilities without access to the underlying code.
- OWASP ZAP: Tests web application security and can identify vulnerabilities in running applications.
- Checkmarx: Identifies vulnerabilities in running applications in real time, providing insights into how an attacker might exploit potential vulnerabilities in a live environment.
Dynamic code analysis with New Relic: Beyond static analysis, New Relic natively provides insights into runtime performance and potential security threats. By monitoring applications in real time, New Relic can identify vulnerabilities that may only become apparent during execution.
Integrating security into the development lifecycle
Importance of secure code management
Code management goes beyond just writing code. Code management is a holistic process, and with New Relic, developers have access to New Relic Security RX features that support version control, patch management, and security best practices. These features ensure that as code evolves, security remains a top priority.
Secure coding in Agile and DevOps environments
In modern development methodologies, there's a growing emphasis on "shift left"—a strategy that integrates security measures right from the beginning of the software development lifecycle. Instead of treating security as a final checkpoint, shift left ensures that security considerations are front and center from the initial design phase onwards.
New Relic fully supports and enhances the shift-left approach. By providing real-time monitoring and feedback, New Relic allows development teams to identify and address potential vulnerabilities early in the development process. This proactive approach not only reduces the risk of security breaches but also leads to more efficient development cycles, as issues are addressed before they become deeply embedded in the code.
Furthermore, New Relic capabilities seamlessly integrate with Agile and DevOps workflows, ensuring that security remains a top priority throughout the entire development and deployment process. Whether it's through automated scans, performance monitoring, or vulnerability assessments, New Relic empowers teams to uphold the principles of shift left and deliver secure, high-quality software at speed.
CI/CD considerations for security
- Automated security scans in CI pipelines: One of the primary benefits of continuous integration (CI) is the ability to automatically test code changes. By integrating automated security scans into CI pipelines, teams can ensure that vulnerabilities are detected early. The New Relic platform can be integrated with popular security scanning tools, like GitHub Dependabot and Aqua Trivy, providing real-time feedback to developers and ensuring that security flaws are addressed before code is merged.
- Secure deployment practices in CD: Continuous deployment (CD) automates the release process, ensuring that new features, fixes, and updates are delivered to users rapidly. However, this speed can be a double-edged sword if security isn't prioritized. With New Relic, teams can monitor deployments in real time, ensuring that no security regressions are introduced. If a vulnerability is detected post-deployment, New Relic monitoring capabilities can provide immediate alerts, allowing teams to react swiftly.
- Environment isolation and security: In CI/CD, it's common to have multiple environments like development, staging, and production. Ensuring that these environments are isolated and secure is crucial. New Relic provides insights into the performance and security posture of each environment, ensuring that potential vulnerabilities in one environment don't compromise another.
- Feedback loops and security insights: A robust CI/CD process is built on feedback loops. Developers need to know the impact of their changes, not just in terms of functionality but also security. New Relic dashboards and alerting mechanisms provide teams with immediate feedback on the security implications of their code changes, fostering a culture where security and performance go hand in hand.
- Integrating threat intelligence into CI/CD: With the ever-evolving landscape of cyber threats, staying updated is crucial. Integrating threat intelligence platforms with CI/CD pipelines can provide real-time insights into emerging vulnerabilities and threats. The New Relic platform can be integrated with threat intelligence tools, ensuring that the development and deployment processes are always informed by the latest security data.
Conclusion
In today's fast-paced digital world, the need to ship code quickly must be balanced with the imperative to keep that code secure. By adhering to best practices, staying updated on the latest security threats, and leveraging cutting-edge tools and technologies, developers can rise to this challenge. New Relic observability and security capabilities offer an integrated solution that makes it easier than ever to ship secure code fast.
Next steps
Ready to elevate your secure coding practices? Register for New Relic for free (up to 100 GB data). and take the first step toward a more secure future.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.