In the dynamic domain of software development, continuous integration and continuous deployment (CI/CD) pipelines are the lifeblood of modern innovation. They seamlessly transform developer code into live applications, but this agility comes with its own set of challenges. As we further rely on CI/CD pipelines, the threat landscape also expands. New Relic is here to guide you through a journey of CI/CD security, ensuring performance, reliability, and—most importantly—trustworthiness.
Understanding CI/CD security
Ensuring CI/CD security means embedding protection mechanisms throughout the automated processes of code integration and deployment. Think of it like this: Your CI/CD pipeline is akin to an expressway where code (vehicles) moves rapidly towards production (destination). Without streamlined security, you risk bumps and breaches. CI/CD security acts as the traffic management system, ensuring smooth and secure progress.
Key aspects of CI/CD security
Guarding sensitive data: With potential access to customer data, API keys, and passwords, it's crucial to seal any breaches. An oversight could mean not just data loss, but trust erosion.
Preserving code integrity: The pipeline is the bastion where your code evolves and matures. Any compromise could infiltrate malicious code into production, jeopardizing user experience and brand credibility.

How to secure your CI/CD pipeline
In a world where the slightest gap in security can lead to significant consequences, it’s essential to approach your CI/CD pipeline as more than a development tool—it's your frontline defense in application security. It’s about crafting a harmonious blend of speed, efficiency, and ironclad security at each phase of your development cycle. Let’s delve deeper into this and explore the practical steps you can employ at every pivotal point in your CI/CD pipeline, transforming it from a mere conveyor belt of code into a well-guarded fortress of innovation.
Development phase
- Champion secure coding: Elevate your team's coding finesse with updated security insights and best practices.
- Harness source code analysis tools: Integrate tools to scan for vulnerabilities right at the code commit stage.
- Stay updated with dependencies: Use real-time scanning to check and refresh third-party libraries.
Integration phase
- Automate security testing: Automatically execute security tests such as with an interactive application security tool (IAST) tool.
- Endorse secure configurations: Guarantee a congruent and secure integration environment.
- Uphold code integrity with signing: Ensure every piece of code is verified and maintains its integrity.
Deployment phase
- Advocate the principle of least privilege (PoLP) strategy: Refine access controls, keeping them minimal and precise.
- Implement distinct secrets management: Protect and differentiate secrets specific to various environments.
- Prioritize pre-deployment reviews: Before the final leap, vet the code for any lurking vulnerabilities.
Post-deployment phase
- Real-time vigilance: Continuously monitor application behavior, receiving alerts for any anomalies with New Relic real-time monitoring.
- Stay adaptive with audits: Consistently revisit and adapt your security strategies.
- Master incident management: Be prepared for contingencies with a foolproof response plan.
By rigorously applying these security measures at every stage of your CI/CD pipeline, you’re not just building software—you’re crafting a fortress of reliability and trust around it. It’s a comprehensive strategy that turns the pipeline into a well-guarded pathway, allowing innovation to flow swiftly and securely to your users. With these sentinels in place, your CI/CD pipeline becomes a model of both efficiency and security, powering your progress with peace of mind.
Level up your CI/CD security
By infusing stringent security measures throughout this pipeline, organizations not only ward off potential threats but also foster a culture of trust and reliability. With New Relic at your side, transforming your CI/CD process into a beacon of efficiency and security becomes an achievable feat. Elevate your development journey, and let innovation and assurance go hand in hand.
Next steps
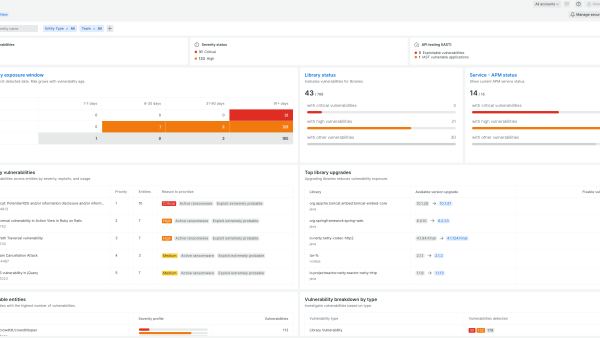
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.