In today's digital world, where companies are racing towards cloud adoption, mobile application security is a pivotal concern. As businesses embrace the cloud, they must also navigate the complex waters of mobile application security. It’s more than just a technical challenge; it’s a fundamental business imperative. In an era where mobile applications are the face of a company’s digital presence, a single security breach can have devastating consequences, not only for the company’s data but also for its reputation and customer trust. Let’s explore how to secure your mobile future.
Understanding mobile application security
As we set sail into the depths of mobile application security, it’s essential to first establish a solid understanding of what this entails. What exactly is mobile application security, and why is it so critical in today’s digital landscape? Moreover, as technology continues to advance at a rapid pace, the threats we face are evolving in tandem. It’s a dynamic and often daunting landscape, but with knowledge as our compass, we can navigate it effectively. In the following sections, we will demystify the concept of mobile application security and take a closer look at the ever-changing landscape of mobile threats and vulnerabilities that developers and businesses must stay ahead of.

What is mobile application security?
Mobile application security is a critical aspect of software development that focuses on the protection of mobile applications from various forms of cyberthreats. In a world where mobile devices are ubiquitous and integral to our daily lives, mobile applications have become prime targets for attackers. Here’s a deeper dive into what mobile application security encompasses:
- Data protection: Guarding users' treasured data—from private info to login details—is paramount. Encryption is our first line of defense.
- Code security: Fortifying the very foundation of the app ensures it stands resilient against cyber-attacks. Practices like code obfuscation and routine reviews bolster its defenses.
- Authentication and authorization: Strong verification processes ensure only the rightful users gain entry, bolstering app sanctity.
- Network security: As apps whisper secrets across the digital expanse, secure communications, like Secure Sockets Layer/Transport Layer Security (SSL/TLS), ensure they aren't overheard.
- OS security: Each mobile OS, be it iOS or Android, carries its own shield and sword. Harnessing these tools while dodging their pitfalls is essential.
- Third-party integrations: Though convenient, third-party components demand vigilance to keep potential vulnerabilities at bay.
- Regulatory adherence: Laws like GDPR and CCPA have set the stage, and apps must perform while staying within the spotlight of compliance.
- Monitoring and response: Vigilance doesn’t end post-deployment. Continuous surveillance and adept response strategies are the backbone of enduring security.
In essence, mobile security isn’t a mere checklist—it's a holistic strategy, weaving security threads throughout the app's lifecycle.
The evolving landscape of mobile threats and vulnerabilities
In the dynamic realm of technology, the only predictable element is change. This rings particularly true when discussing the ever-shifting arena of mobile threats and vulnerabilities. As mobile devices play an increasingly pivotal role in both our personal and professional spheres, they consequently become prime targets for cyber adversaries. Let's delve deeper into the nuances of this transformative landscape:
- Sophisticated malware attacks: The notion of straightforward, detectable malware is a thing of the past. Contemporary malware designs are intricate, leveraging state-of-the-art techniques to sidestep detection and unleash their payload. Instances range from ransomware holding user data hostage to covert spyware observing and transmitting personal information.
- Phishing and social engineering attacks: Digital attackers craft deceptively genuine phishing messages, compelling users to unwittingly disclose sensitive details, from login particulars to financial credentials.
- Insecure data storage and transmission: With a surge in user data collection and transfer, the impending risks of data leaks amplify. Cyber adversaries are on a perennial quest to exploit such vulnerabilities.
- Exploiting operating system vulnerabilities: Each iteration of mobile OS, whether it's iOS or Android, might bring along potential security weak points. Attackers pounce on these openings swiftly, often faster than patches are deployed.
- Rogue third-party libraries and components: While third-party resources offer convenience, they're not without their share of threats. An ostensibly secure app can be undermined by a compromised external component.
- API and backend attacks: As mobile apps interface with backend platforms via APIs, attackers are increasingly setting their sights on these communication bridges.
- Device and network-level attacks: Not just content with targeting applications, attackers are also turning their attention to the very devices and networks these apps rely on.
- Emerging threats from new technologies: As we welcome advancements like IoT, 5G, and sophisticated AI into the mobile app ecosystem, we also usher in fresh vulnerabilities.
- Regulatory and compliance challenges: Evolving privacy legislations make maintaining compliance, alongside robust security, a complex endeavor.
- Supply chain attacks: These assaults focus on the software supply chain's weak links, encompassing integrated third-party services and tools.
In this dynamic domain, perpetual alertness and adaptability are pivotal. It's imperative for all stakeholders—from developers to entire organizations—to remain attuned to emerging threats, proactively refining their security blueprints in tandem.
The challenges of mobile application security
Traversing the multifaceted world of mobile application security is reminiscent of navigating a labyrinth. The route is fraught with mutating threats, varied user habits, and the relentless pace of tech evolution. Here's a snapshot of the predominant challenges faced:
- Keeping up with evolving threats: The cyberthreat milieu is anything but stagnant, demanding consistent vigilance from security aficionados.
- Diverse device and OS ecosystem: Achieving consistent security across the vast expanse of devices and operating systems is no small feat.
- User behavior and education: Unintentional missteps by users—from frail passwords to susceptibility to phishing ruses—often end up compromising security.
- Third-party libraries and components: Leveraging third-party assets is a double-edged sword, offering development agility at the potential expense of security.
- Resource constraints: While security necessitates dedicated resources, not every organization can readily allocate them, especially the smaller entities.
- Regulatory compliance: The regulatory terrain, with its myriad data protection mandates, presents a constantly evolving puzzle for compliance.
- Rapid development cycles: The breakneck speed of contemporary tech development can sometimes sideline security, elevating vulnerability risks.
- Monitoring and incident response: Establishing a vigilant monitoring mechanism, complemented by a cogent incident response blueprint, is easier said than done.
- Integrating security into DevOps (DevSecOps): Incorporating security within the DevOps continuum, without hampering the development cadence, demands a delicate balancing act.
- Supply chain attacks: Ensuring impregnable security across the software supply chain, from utilities to third-party services, is an escalating challenge.
However, with a judicious, informed, and proactive approach, these challenges can be effectively surmounted. Security in mobile application development is an ongoing pact, necessitating unwavering attention throughout the app's lifecycle.
Overcoming challenges with mobile application security best practices
Although the intricacies of mobile application security might seem daunting, they're far from undefeatable. Through judicious strategy and proactive execution, organizations can fortify their mobile applications against threats. Here are essential tactics to weave into your approach:
- Embrace a security-first culture: Infuse security into every stage of your app's journey, from conceptualization to deployment.
- Regular security audits and assessments: Periodic in-depth security evaluations, encompassing code scrutiny and vulnerability assessments, are indispensable.
- Educate and train your team: Arm your teams with the latest in security knowledge and best practices.
- Implement strong authentication and authorization: Employ robust multi-layered authentication techniques, complemented by meticulous authorization protocols.
- Encrypt sensitive data: Unwavering encryption for data, whether in transit or at rest, is non-negotiable.
- Regularly update and patch systems: Vigilance in timely updates ensures you're shielded from known threats.
- Leverage mobile security frameworks and tools: Harness the power of recognized mobile security frameworks to bolster application defenses.
- Monitor and log application activity: A meticulous logging and monitoring setup can be your first line of defense against potential threats.
- Develop and practice an incident response plan: A diligently crafted incident response blueprint, coupled with regular drills, ensures seamless threat mitigation.
- Adopt DevSecOps practices: Seamlessly integrate security within your DevOps narrative.
- Stay informed and adapt: With the fluid nature of the security domain, a commitment to constant learning and adaptability is pivotal.
By embracing these strategies, organizations can sculpt a resilient security posture that evolves in sync with the fluid landscape of threats. It's a journey of proactive engagement, embedding security at the heart of organizational culture and app development endeavors.
Where mobile application security testing comes into play
As you embark on developing feature-rich apps that handle delicate user data, ensuring their fortress-like defense against threats becomes non-negotiable. Mobile application security testing isn't just a line item—it's your frontline defense. With such testing, you delve deep into the app's very fabric, bringing to light any vulnerabilities that might have sneaked in unnoticed. It's about reinforcing data safeguards, solidifying every user interaction, and guaranteeing uncompromised data flows. Remember, with the right testing approach, it isn't merely about spotting vulnerabilities but embracing a strategy that empowers you to proactively fortify your app.
Secure your future with New Relic IAST
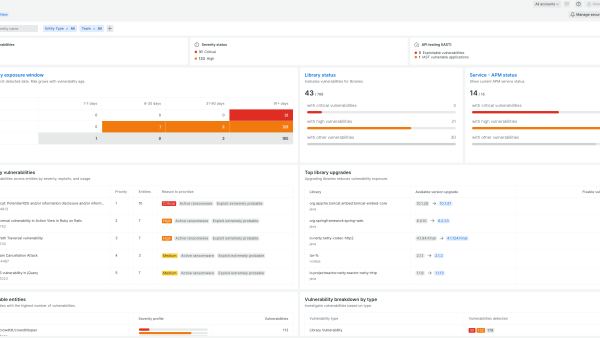
At New Relic, we're all about innovation and proactive solutions. Enter New Relic IAST—our latest offering in the realm of application security. IAST, or interactive application security testing, serves as your insider view into your apps' operational terrain. Think of it as a magnifying lens that meticulously combs through your app, from the inside out, while it's running in its natural environment. This real-time data capture offers unparalleled insights into potential security hitches, providing a hybrid advantage of both static and dynamic application security testing. With New Relic IAST, you're not only spotting vulnerabilities but understanding them in the context of your app's typical workflow. It's not just about identifying weaknesses; it's about truly comprehending their impact and rectifying them in real time. Dive deep, gain clarity, and propel your app's security to new heights, all under the trusted umbrella of New Relic.
Next steps
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.