Securing software applications has shifted from optional to essential. As cyber threats diversify and multiply, our defenses must mature. Interactive application security testing (IAST) emerges, fusing the strengths of static and dynamic testing. It perfectly fits the integrated ethos of DevSecOps—merging development, security, and operations. Let's navigate the intricacies of IAST and harness its power for robust DevSecOps.
The rise of IAST
As applications become more complex, the need for effective and efficient security testing has surged. IAST is a solution that monitors applications from within, observing how data flows through the system in real time, and spotting vulnerabilities before they can be exploited. It’s the proactive and dynamic answer to the reactive and static methods of the past, heralding a new era in application security.
The significance of DevSecOps
Security has evolved from a mere stage to the backbone of software development. Here, DevSecOps takes the center stage. A refined version of the DevOps mantra, DevSecOps ingrains security right from the get-go. This strategy doesn't just shield applications—it cultivates a security-first mindset.
Core concepts of DevSecOps
At the heart of DevSecOps lie foundational principles that redefine the software development paradigm, emphasizing that security isn't just a feature, but the very fabric of the process. Let’s take a look at the bones of DevSecOps.
- Shifting security left: Prioritize security from day one for timely vulnerability detection.
- Security is everyone’s game: DevSecOps thrives on collective accountability—developers, operations, and security teams.
- Always-on security monitoring: With DevSecOps, security is a 24/7 commitment.
- Automated yet sharp: Streamline security checks for consistency and efficiency.
The DevSecOps lifecycle
Navigating the software development journey, the DevSecOps lifecycle intricately weaves security into every phase. Let’s uncover what that looks like.
- Planning: Security objectives lead, even before the first line of code.
- Secure coding: Developers adhere to fortified coding guidelines.
- Integrated security checks: As integration occurs, security tests flag early vulnerabilities.
- Safe deployment: Ensure a secure environment and vulnerability-free new codes.
- Continuous vigilance: Security tools actively scan while logs identify potential risks.
- Periodic audits: Regular checks ensure robust security measures and compliance.
- Full-throttle testing: Blend automated tools and manual tests for comprehensive scrutiny.
Embedding IAST into DevSecOps
Fusing IAST into DevSecOps isn't plug and play—it's strategic. It's about aligning your IAST tool with your overall vision. While there's no universal blueprint, here's a roadmap to guide your IAST integration journey:
- Outline needs: Define your IAST expectations.
- Pick your IAST tool: Sync with your organization’s tech requirements.
- Embed IAST in CI/CD: Seamlessly introduce IAST into your continuous integration and continuous deployment (CI/CD).
- Tune and personalize: Align the tool with your unique application design and security rules.
- Upskill your squad: Ensure everyone is well-versed with the IAST nuances.
- Stay attuned: Regularly review the IAST output and recalibrate if needed.

Why IAST in DevSecOps matters
Embedding IAST into DevSecOps is akin to enhancing your development's IQ. It's not just about flagging risks—it's about understanding the security pulse in real time. The benefits? Let's touch on a few key highlights:
- Instant feedback: IAST operates live, immediately spotlighting vulnerabilities.
- Fewer false alarms: IAST smartly filters genuine threats from benign anomalies.
- Early issue spotting: Early detection translates to swift, cost-effective solutions.
- Smooth compliance: Simplify audits with IAST's automatic compliance checks.
- Empowered developers: With instant feedback, developers adapt faster and more confidently.
However, integrating IAST isn't without its challenges. Proper tool selection, data management, and team training are critical components to nail.
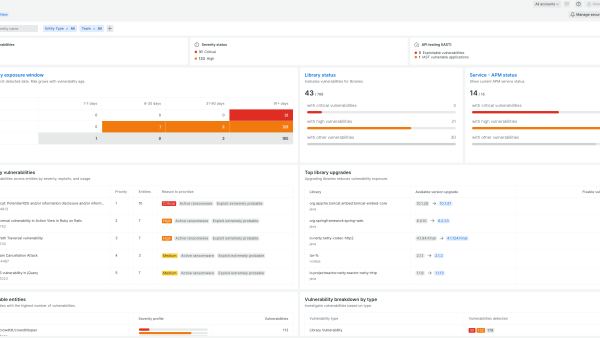
Meet New Relic IAST
Designed for developers, New Relic IAST is intuitive and potent. It aligns seamlessly with DevSecOps, delivering real-time, actionable insights. With New Relic IAST, developers can dream and code big, backed by top-tier security intelligence.
New Relic IAST isn’t just a tool—it’s your security ally, epitomizing the DevSecOps ethos of integrated security.
Together, New Relic and IAST are setting the stage for faster, safer software deployment. Secure your future with us.
Next steps
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.