In this digital sprint where everyone is rushing to innovate, securing our apps becomes the finish line we all need to cross. But how can developers ensure the software they deliver is not only cutting-edge but also fortified against security vulnerabilities? The answer lies in secure code reviews.
What is a secure code review?
Dive deep into the software development realm and you'll find the secure code review. This is where developers or our trusty security experts sift through source code to spot and fix potential vulnerabilities. While traditional code reviews might focus on the tune of functionality and performance, secure code reviews play a different note—prioritizing security best practices and sidelining potential risks.
The need for secure code reviews in application development
In a world where cyberattacks are becoming the norm, leaving security as an afterthought can come at a hefty price. From staggering financial hits to eroding trust, the impact is vast. But, with secure code reviews, you get to design with security at the heart of it—drastically reducing vulnerabilities that might otherwise slip through.
Components of secure code reviews
Embarking on a secure code review? Here’s what you should be looking at:
- Authentication and authorization: Is the system intuitive enough to recognize and manage user permissions effectively?
- Input validation: Does it have an eagle eye for incoming data, ensuring no malicious injections take place?
- Session management: How well are user sessions guarded against potential threats?
- Error handling: Can the application handle hiccups without spilling any secrets?
- Cryptography: Does it understand the nuances of encryption and hashing?
A look into the secure code review process
Take a step-by-step journey through the secure code review process:
- Scope definition: Pinpoint the code sections up for review.
- Static analysis: Employ tools to scan and ensure code is on point and secure.
- Manual review: This is where human intuition comes in to find complex vulnerabilities.
- Feedback and remediation: Relay the findings to the developers for tweaks and improvements.
- Re-testing: Round two of checking to ensure everything's shipshape.

15-step secure code review checklist
Here's a handy checklist to guide your secure code review journey. Remember, these are broad strokes—tailor them to fit the nuances of your project.
1. Authentication and authorization
- Are all authentication mechanisms robust, utilizing strong cryptographic practices?
- Is there a system in place to manage, rotate, and expire passwords?
- Does the application prevent brute-force attacks?
- Are roles and permissions correctly implemented to ensure only authorized users can access certain functions?
2. Input validation
- Are all user inputs validated and sanitized to prevent injection attacks (for example, SQL, XML, and OS command injections)?
- Is there a mechanism to check and reject inputs with unnecessary special characters or overly large inputs?
3. Output encoding
- Does the application properly encode outputs to prevent cross-site scripting (XSS) attacks?
- Are there mechanisms to safely generate dynamic web pages and prevent content spoofing?
4. Session management
- Are session IDs securely generated and hard to predict?
- Does the application implement an inactivity session timeout?
- Is the "secure" flag set for HTTPS cookies?
5. Error handling
- Does the application handle errors without revealing sensitive information?
- Are system-level error messages caught and redirected to custom error pages?
6. Data protection
- Are sensitive data (passwords, credit card numbers, health data, etc.) encrypted both at rest and in transit?
- Does the system limit exposure of sensitive data only to those who need it?
7. Business logic
- Can users manipulate variables (for example, prices and user levels) to bypass business logic?
- Are there any checks and balances in place to prevent fraud or data corruption?
8. Code and architecture analysis
- Is the code structured in a modular and maintainable way?
- Does the codebase avoid deprecated libraries or APIs known to be vulnerable?
9. API security
- Are there protections against distributed denial of service (DDoS) attacks?
- Are rate limits in place for API requests to prevent abuse?
- Is data being validated before being processed by the API endpoints?
10. Third-party libraries and dependencies
- Are all third-party libraries, plug-ins, and other dependencies up to date?
- Are they sourced from trustworthy repositories?
- Have they been audited for known vulnerabilities?
11. File and resource management
- Does the application check file types and sizes before uploads?
- Are files scanned for malware or malicious content before being processed?
- Are insecure direct object references (IDOR) prevented?
12. Logging and monitoring
- Does the system log security-relevant events, such as failed login attempts or data access anomalies?
- Are logs protected from tampering and unauthorized access?
- Is there an alerting system in place for suspicious or malicious activity?
13. Configuration management
- Are default usernames and passwords changed?
- Are unused features and ports disabled or removed?
- Is the software kept up to date with patches?
14. Encryption and cryptography practices
- Is encryption used for data in transit and at rest using strong algorithms?
- Are cryptographic keys stored and managed securely?
- Is there a protocol for key rotation?
15. Code review and testing processes
- Is there a systematic and periodic code review process in place?
- Are there automated tests, including security tests, in the CI/CD pipeline?
- Are test results reviewed and acted upon?
Challenges of implementing secure code reviews in the SDLC
While secure code reviews hold the promise of fortified apps, blending them into the software development lifecycle (SDLC) brings its own set of hurdles:
- Time: Secure reviews can demand time, often slowing down the rhythm of releases.
- Skills: The expertise to conduct a precise secure review isn't universal.
- False alarms: Sometimes, automated tools might get it wrong, flagging harmless code.
Automating your secure code review journey
In this evolving tech landscape, automating secure code reviews stands as a beacon. By harnessing automated tools, vast code terrains can be scoured for security glitches, offering a proactive approach. With automation, we're talking about consistency, scalability, and feedback that's almost instantaneous.
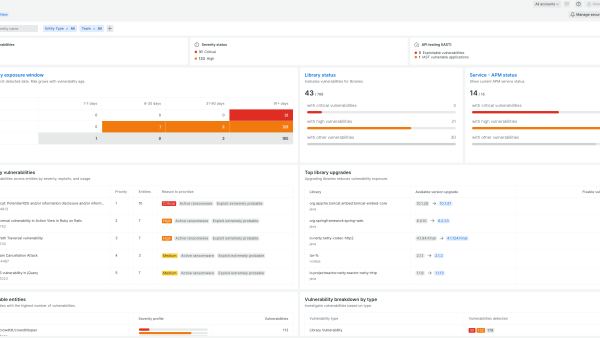
While human expertise has its irreplaceable charm, capabilities like New Relic interactive application security testing (IAST) amplify the secure review process. With New Relic IAST, the application gets a real-time security scan, offering insights that seamlessly blend into the development rhythm.
Next steps
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.