In our fast-paced, interconnected world, application security isn't just a luxury—it's essential. As the cyberattack landscape grows, businesses can't afford to let security slide. Let's dive into the top 15 best practices you should be adopting for your application's security.
The challenges of maintaining application security
The digital terrain shifts constantly. Between rapid tech innovations and new cyber threats, ensuring application security becomes a monumental task. Consider this: each application component can have exploitable vulnerabilities. Add to this the limited resources and expertise, and it's evident why security deserves your utmost attention.

Comprehensive application security best practices checklist
Here's a checklist of 15 best practices that can help you enhance your application's security:
1. Stay ahead with regular security audits
Delve deep into your application's security structure regularly. Identify vulnerabilities, assess your security strategies, and stay compliant. With methods like automated scanning and manual code checks, you'll spot and squash vulnerabilities before they're an issue.
2. Level up with secure coding techniques
Shield your code from malicious attackers. Adopt techniques that validate input and encode output, thus avoiding potential exploit avenues like XSS.
3. Use trusted security frameworks and libraries
Save time and leverage the expertise of security aficionados. With established security frameworks and libraries, you ensure efficient, reliable security measures.
4. Keep it secret, keep it safe: Encrypt sensitive data
Encryption, both at rest and in transit, is your go-to for safeguarding essential data from prying eyes.
5. Handle errors with finesse
Ensure that error messages give away nothing. Implement strategies that provide users with generic messages while logging the intricate details for internal checks.
6. Stay current with updates and patches
Regular updates shield you from known vulnerabilities. Keep an updated software inventory and apply patches diligently.
7. Embrace minimalism with the principle of least privilege (PoLP)
Limit access to ensure security. Streamline roles, restrict unnecessary permissions, and guard against potential misuse.
8. Shift-left and shine with DevSecOps
Integrate security from day one of development. Make it a collective team responsibility, resulting in quicker vulnerability detection and application fortifications.
9. Protect yourself with a web application firewall
A web application firewall (WAF) provides a protective layer between your application and potentially harmful traffic. It monitors and filters HTTP traffic to and from the application. WAFs can help defend against many common web attacks such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF) by identifying and blocking malicious requests.
10. Organize continuous security training sessions
Keep your team updated and empowered. Regular training sessions ensure they're always ready to counter evolving threats.
11. Build security into every phase with SDLC
From design to maintenance, embed security checks and practices into every stage of your software development lifecycle (SDLC).
12. Regularly back up data
Regularly back up data, encrypt it, and test its recovery. This way, you're always prepared for the unexpected.
13. Develop an incident response plan
Be ready to act swiftly and efficiently in case of a breach. An effective incident response process (IRP) helps minimize damage, protect your brand, and stay compliant.
14. Design with foresight: Incorporate threat modeling
Early-stage threat modeling means you're proactively building a robust security foundation.
15. Harness the power of container security
In a container-driven development world, ensure you've tailored security measures for these unique environments.
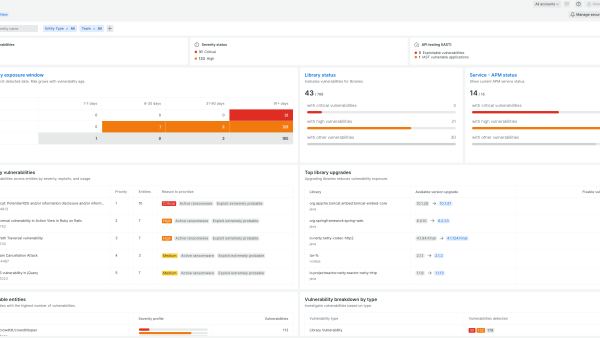
Secure tomorrow, today with New Relic
Why wait for a breach to prioritize security? With New Relic interactive application security testing (IAST) you can get ahead of potential threats. In today's digital landscape, customer trust is gold. Secure your applications with New Relic and stay golden. Don't wait—fortify your application defenses with New Relic now!
Next steps
Learn more about New Relic IAST.
Sign up for a free account today to take advantage of IAST and the 30+ other capabilities of the New Relic platform. Your free account offers 100 GB/month of data ingest, one full-platform user who can use all of our tools, and unlimited basic users who can view your data and insights.
The views expressed on this blog are those of the author and do not necessarily reflect the views of New Relic. Any solutions offered by the author are environment-specific and not part of the commercial solutions or support offered by New Relic. Please join us exclusively at the Explorers Hub (discuss.newrelic.com) for questions and support related to this blog post. This blog may contain links to content on third-party sites. By providing such links, New Relic does not adopt, guarantee, approve or endorse the information, views or products available on such sites.