Why try Security RX?
Trusted by customers across industries.
- De vraies informations pratiques sur votre stack
- Dépannage de l'infrastructure en amont
- Des dashboards, alertes et intégrations en un seul et même endroit
- Intégration rapide de centaines d'outils et normes open source
- Payez à l'utilisation sans devoir acheter de logiciels inutiles ni payer de pénalités de dépassement
Powerful tools
that show powerful results
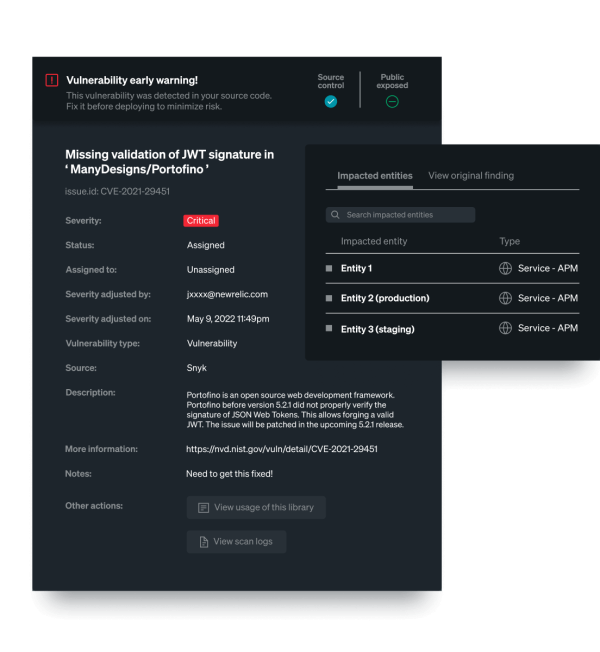
SECURE SOFTWARE DEVELOPMENT
Be more secure from the first line of code.
- Identify vulnerabilities automatically within third-party libraries.
- See recommended library upgrades in APM services based on known CVEs.
- Get continuous monitoring for immediate results and faster fixes.
CONTINUOUS SOFTWARE COMPOSITION ANALYSIS
Boost development velocity.
- Accelerate your CI/CD pipeline. Know what goes into applications without constantly scanning.
- Detect vulnerabilities in runtime in minutes, not days.
- Prioritize potential exploits in supporting libraries for a more secure development lifecycle.


SECURITY FOR EVERYONE
Improve team collaboration around security.
- Stop accidental vulnerabilities. Unify security insights for DevOps, SREs, and InfoSec teams.
- Align teams on the operational and business risks of potential security incidents.
- Prevent breaches by known vulnerabilities and lower security risks across your stack.
SECURITY WORKFLOWS
Stop juggling priorities with multiple tools.
- Put development, operations, and security teams in sync.
- Prioritize, track, and report vulnerabilities at the organization, team, or component level.
- Improve handovers with automated risk scores that feed into DevOps workflows.

Regardez qui aime nos produits.
1
